Did you know that passing the Microsoft Azure AZ-500 exam requires good help? AZ-500 dumps latest online is the Microsoft Azure Secure Technology exam learning helper that helps you prepare for the AZ-500 exam with ease.
The latest update of the AZ-500 dumps Q&A material is a great learning helper. Get the AZ-500 dumps Webpage: https://www.pass4itsure.com/az-500.html (364+ Q&As) can help you successfully pass the Microsoft Azure Security Technologies exam.
What are the key points of the Microsoft Azure Security Technologies exam?
Microsoft Azure Security Technologies, also known as the AZ-500 exam, is an exam affiliated with Microsoft Certified: Azure Security Engineer Associate that earns you the certification. The passing score of the exam is 700. Available in English, Japanese, Chinese (Simplified), Korean, German, French, Spanish, Portuguese (Brazil), Arabic (Saudi Arabia), Russian, Chinese (Traditional), Italian, and Indonesian (Indonesia), the exam fee is $165.
Focus on the following
- Manage identity and access
- Implement platform protection
- Manage security operations
- Secure data and applications
Specially prepared for you effective AZ-500 exam study resources:
- AZ-500: Manage Identity and Access
- AZ-500: Implement platform protection
- AZ-500: Secure your data and applications
- AZ-500: Manage security operation
- Pass4itSure AZ-500 dumps
How do I prepare for the Microsoft certification AZ-500 exam?
To take the Microsoft Certified AZ-500 exam, the updated Pass4itSure AZ-500 dumps are the best learning helper. It provides AZ-500 exam Q&A materials that will help you successfully pass the Microsoft Azure Security Technologies exam.
Download the AZ-500 questions (free) to help you prepare for the exam: https://drive.google.com/file/d/1uvPz9I1g-uhxYQIO3-q4rtvYwYU2DQtH/view?usp=sharing
Free Microsoft Azure Security Technologies AZ-500 Dumps Update Q&As
1. You have an Azure Active Directory (Azure AD) tenant and a root management group. You create 10 Azure subscriptions and add the subscriptions to the root management group. You need to create an Azure Blueprints definition that will be stored in the root management group. What should you do first?
A. Add an Azure Policy definition to the root management group.
B. Modify the role-based access control (RBAC) role assignments for the root management group.
C. Create a user-assigned identity.
D. Create a service principal.
Correct Answer: B
Reference: https://docs.microsoft.com/en-us/azure/role-based-access-control/elevate-access-global-admin
2. HOTSPOT
You have an azure active Directory (Azure AD) tenant that contains the resources shown in the following table.
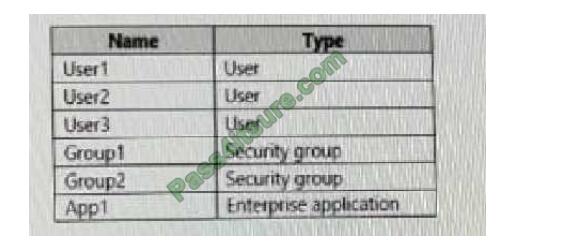
User2 is the owner of Group2.
The user and group settings for App1 are configured as shown in the following exhibit.
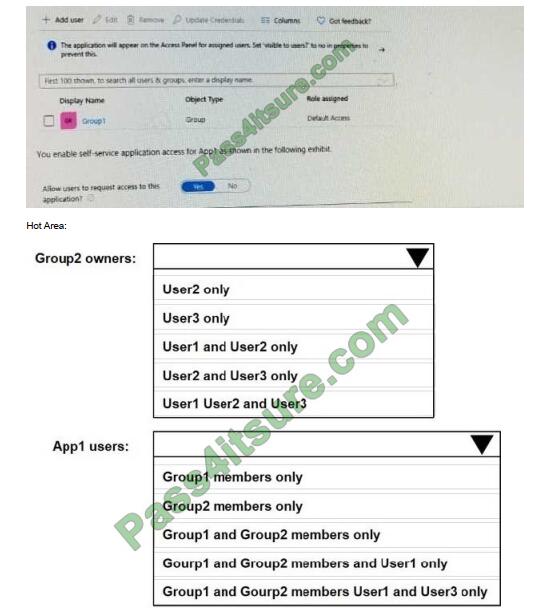
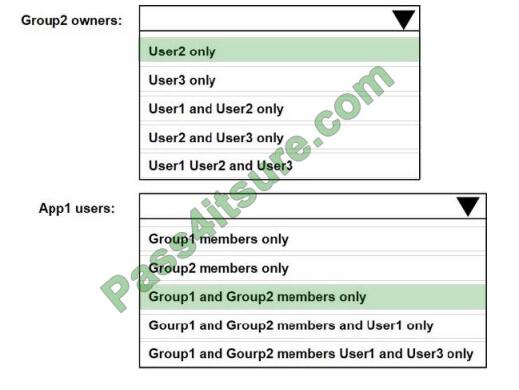
Correct Answer:
3. You have two Azure virtual machines in the East US2 region as shown in the following table.
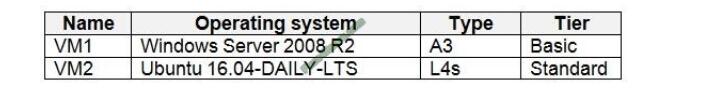
You deploy and configure an Azure Key vault. You need to ensure that you can enable Azure Disk Encryption on VM1 and VM2. What should you modify on each virtual machine? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Hot Area:
Correct Answer:
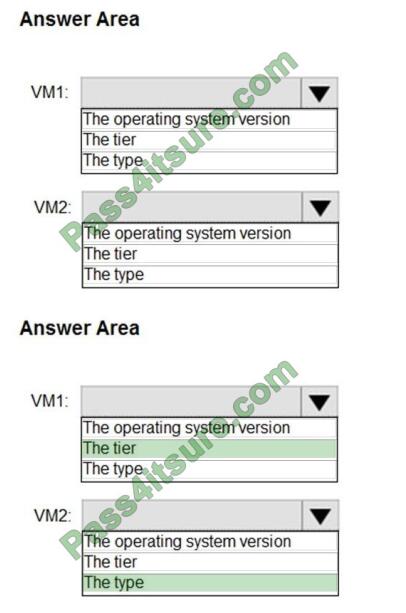
VM1: The Tier
The Tier needs to be upgraded to standard.
Disk Encryption for Windows and Linux IaaS VMs is in General Availability in all Azure public regions and Azure Government regions for Standard VMs and VMs with Azure Premium Storage.
VM2: The type
Need to change the VM type to any of A, D, DS, G, GS, F, and so on, series IaaS VMs.
Not the operating system version: Ubuntu 16.04 is supported.
References:
https://docs.microsoft.com/en-us/azure/security/azure-security-disk-encryption-overview
https://docs.microsoft.com/en-us/azure/security/azure-security-disk-encryption-faq#bkmk_LinuxOSSupport
4. You have an Azure SQL database. You implement Always Encrypted. You need to ensure that application developers can retrieve and decrypt data in the database. Which two pieces of information should you provide to the developers? Each correct answer presents part of the
solution. NOTE: Each correct selection is worth one point.
A. a stored access policy
B. a shared access signature (SAS)
C. the column encryption key
D. user credentials
E. the column master key
Correct Answer: CE
Always Encrypted uses two types of keys: column encryption keys and column master keys. A column encryption key is used to encrypt data in an encrypted column. A column master key is a key-protecting key that encrypts one or more column encryption keys.
5. You are evaluating the effect of the application security groups on the network communication between the virtual machines in Sub2. For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
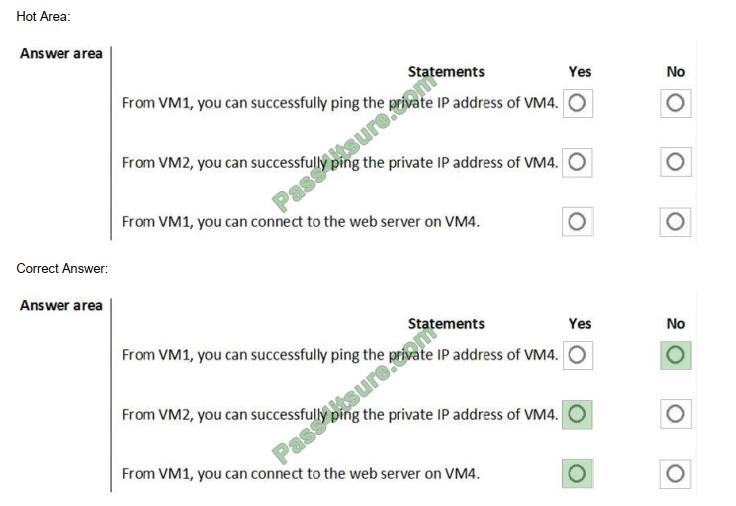
Box 1: No. VM4 is in Subnet13 which has NSG3 attached to it.
VM1 is in ASG1. NSG3 would only allow ICMP pings from ASG2 but not ASG1. Only TCP traffic is allowed from ASG1. NSG3 has the inbound security rules shown in the following table.
Box 2: Yes.
VM2 is in ASG2. Any protocol is allowed from ASG2 so ICMP ping would be allowed.
Box3. VM1 is in ASG1. TCP traffic is allowed from ASG1 so VM1 could connect to the web server as connections to the web server would be on ports TCP 80 or TCP 443.
6. You have an Azure subscription that contains a virtual network. The virtual network contains the subnets shown in the following table.
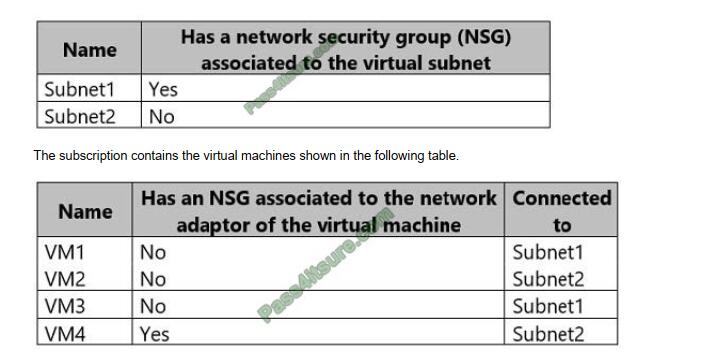
You enable just-in-time (JIT) VM access for all the virtual machines. You need to identify which virtual machines are protected by JIT. Which virtual machines should you identify?
A. VM4 only
B. VM1 and VM3 only
C. VM1, VM3, and VM4 only
D. VM1, VM2, VM3, and VM4
Correct Answer: C
An NSG needs to be enabled, either at the VM level or the subnet level.
Reference: https://docs.microsoft.com/en-us/azure/security-center/security-center-just-in-time
7. You are configuring and securing a network environment. You deploy an Azure virtual machine named VM1 that is configured to analyze network traffic. You need to ensure that all network traffic is routed through VM1. What should you configure?
A. a system route
B. a network security group (NSG)
C. a user-defined route
Correct Answer: C
Although the use of system routes facilitates traffic automatically for your deployment, there are cases in which you want to control the routing of packets through a virtual appliance. You can do so by creating user-defined routes that specify the next hop for packets flowing to a specific subnet to go to your virtual appliance instead, and enable IP forwarding for the VM running as the virtual appliance.
Note: User Defined Routes
For most environments, you will only need the system routes already defined by Azure. However, you may need to create a routing table and add one or more routes in specific cases, such as:
1. Force tunneling to the Internet via your on-premises network.
2. Use of virtual appliances in your Azure environment.
3. In the scenarios above, you will have to create a routing table and add user-defined routes to it.
8. HOTSPOT
You have an Azure subscription that contains an Azure key vault named ContosoKey1. You create users and assign them roles as shown in the following table.
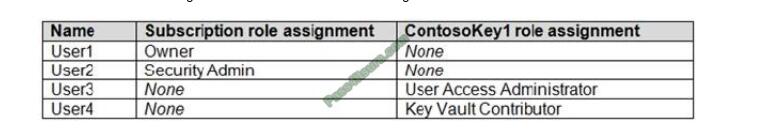
Correct Answer:
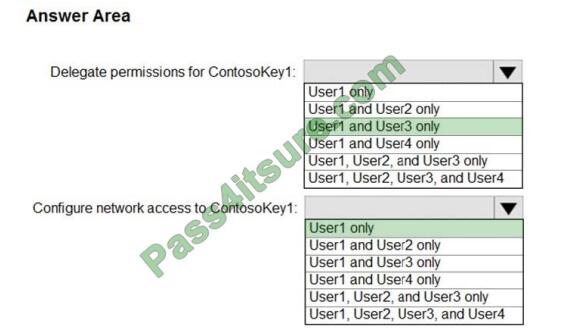
Reference: https://docs.microsoft.com/en-gb/azure/key-vault/general/rbac-guide
9. You need to create Role1 to meet the platform protection requirements. How should you complete the role definition of Role1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
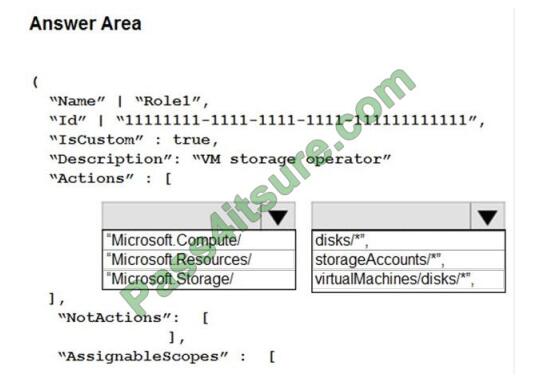
Correct Answer:
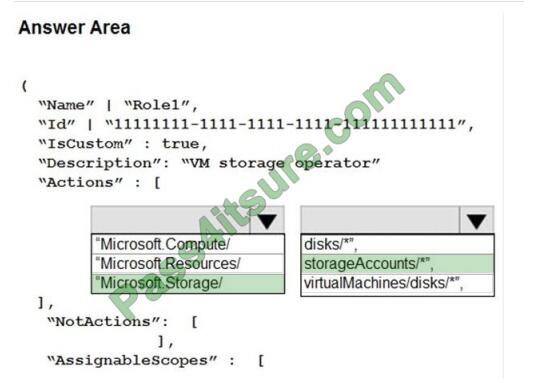
Scenario: A new custom RBAC role named Role1 must be used to delegate the administration of the managed disks in Resource Group1. Role1 must be available only for Resource Group1.
Azure RBAC template managed disks “Microsoft.Storage/”
10. SIMULATION The developers at your company plan to publish an app named App11641655 to Azure.
You need to ensure that the app is registered to Azure Active Directory (Azure AD). The registration must use the signon URLs of https://app.contoso.com. To complete this task, sign in to the Azure portal and modify the Azure resources.
A. See the below.
Correct Answer: A
Step 1: Register the Application
1. Sign in to your Azure Account through the Azure portal.
2. Select Azure Active Directory.
3. Select App registrations.
4. Select New registration.
5. Name the application App11641655. Select a supported account type, which determines who can use the application. Under Redirect URI, select Web for the type of application you want to create. Enter the URI: https://app.contoso.com, where the access token is sent to.
6. Click Register
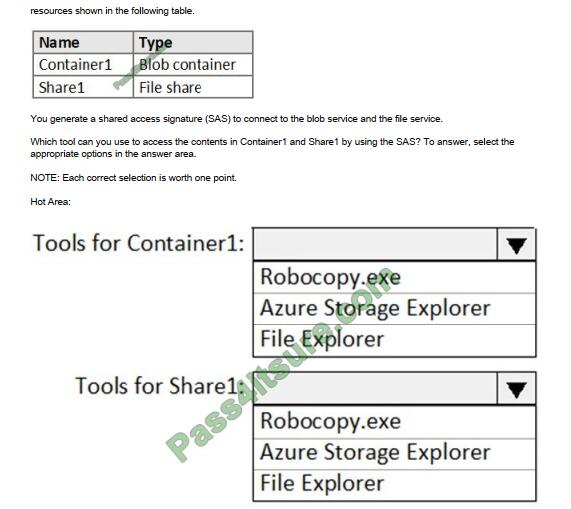
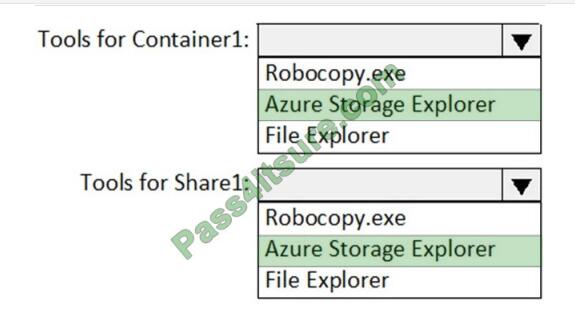
11. HOTSPOT You have an Azure subscription named Sub1. Sub1 has an Azure Storage account named storage1 that contains the resources shown in the following table.
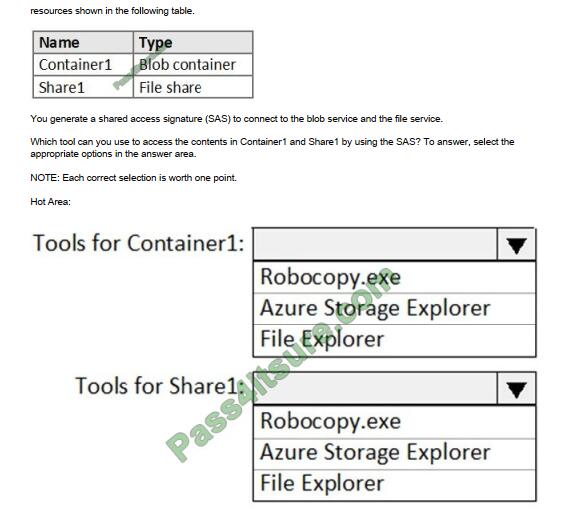
Correct Answer:
12. HOTSPOT You plan to use Azure Sentinel to create an analytic rule that will detect suspicious threats and automate responses. Which components are required for the rule? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Hot Area:
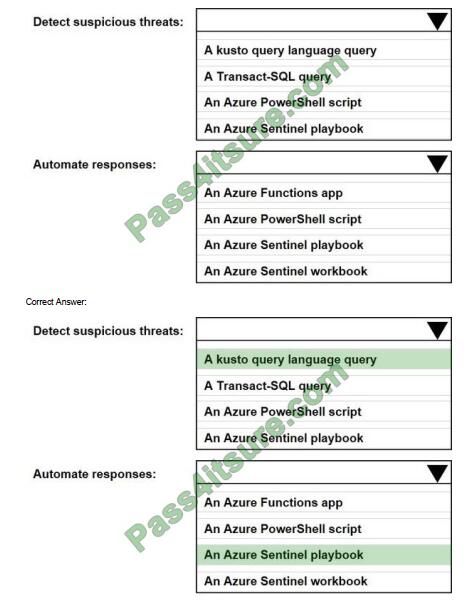
Reference: https://docs.microsoft.com/en-us/azure/sentinel/tutorial-detect-threats-custom https://docs.microsoft.com/en-us/azure/sentinel/tutorial-respond-threats-playbook
13. SIMULATION
You need to ensure that the events in the NetworkSecurityGroupRuleCounter log of the VNET01-Subnet0-NSG network security group (NSG) are stored in the logs11597200 Azure Storage account for 30 days. To complete this task, sign in to the Azure portal.
A. See the below.
Correct Answer: A
You need to configure the diagnostic logging for the NetworkSecurityGroupRuleCounter log.
1. In the Azure portal, type Network Security Groups in the search box, select Network Security Groups from the search results then select VNET01-Subnet0-NSG. Alternatively, browse to Network Security Groups in the left navigation pane.
2. In the properties of the Network Security Group, click on Diagnostic Settings.
3. Click on the Add diagnostic setting link.
4. Provide a name in the Diagnostic settings name field. It doesn\’t matters what name you provide for the exam.
5. In the Log section, select NetworkSecurityGroupRuleCounter.
6. In the Destination details section, select Archive to a storage account.
7. In the Storage account field, select the logs11597200 storage account.
8. In the Retention (days) field, enter 30.
9. Click the Save button to save the changes.
Summarize
AZ-500 dumps question and answer online at https://www.pass4itsure.com/az-500.html to help with exam preparation. It’s your Microsoft Azure Security Technologies Exam Learning Helper.